Homepage » Alt Awareness technology » Employee Security Index
What is the Employee Security Index (ESI®)?
The ESI® is a security awareness indicator and makes the IT security awareness of your employees measurable. It was developed scientifically, has been granted a patent and offers a high degree of comparability and reliability due to its standardisation.
What are you secure against, under what conditions and to what degree? This question brings great challenges when it comes to securing the company and making investment decisions. For the area of social engineering and phishing awareness, IT-Seal has developed a benchmark: the “Employee Security Index” (ESI®).
The Employee Security Index is based on a standardized framework that takes different types of attackers into account by simulating many different attacks with different preparation times. For this purpose, hundreds of different attacks with varying levels of difficulty are created and sent (patented) fully automatically. We make sure that each participant receives a different e-mail to prevent watercooler conversations – which effectively increases security but falsifies the measurement considerably.
Play Video
Our founder and CEO, David Kelm, explains the ESI®
The granting of the patent underlines the scientific approach as well as the uniqueness of the ESI®, as a control instrument for measuring and monitoring security awareness in companies!
Play Video
ESI® – the scientific benchmark for measuring security awareness.
Why are we doing this?
Individual phishing simulations are quickly misleading: click rates can vary greatly from e-mail to e-mail – this is especially true when internal information is used. Depending on the subject, writing style, specific sending time, design or sender, employees either click quickly or not at all. It is easy to create a phishing e-mail that 80 percent of employees click on or one that only 2 percent fall for. However, this does not give any indication of how good the employees really are, but only about how well the phishing e-mail fitted the bill.
In order to be able to make a statement about how good the security behavior of the employees really is, it is necessary to carry out a large number of different attack simulations. This is the only way to filter out individual “lucky hits”. The results of these many different attacks are summarised accordingly in the ESI® and clarified in the form of traffic light signal colours.
How does the Employee Security Index (ESI®) work?
The ESI® makes security awareness training measurable based on scientific data.
Standardization as the basis for measurability
In order to make security awareness measurable, a realistic simulation of attacks is indispensable. Individual attacks should also be comparable with each other – only then can a measurement over a longer period of time provide information about the development of security awareness.
In order to make social engineering attacks comparable, we classify them into different categories. The decisive factor here is the preparation time that a criminal must invest in the preparation and execution of an attack scenario.
This consists, for example, of the procurement of information (OSINT), technical preparation, copying of designs (clone phishing), and keeping the infrastructure ready. Thus, five categories can be divided, which correspond to a preparation time of approx. 1, 3, 10, 20 and 40 hours respectively.
Procedure for determining the ESI®
- Each member of a staff group receives several individual spear phishing e-mails at different levels of difficulty
- The reaction (security behaviour) of the employees is measured
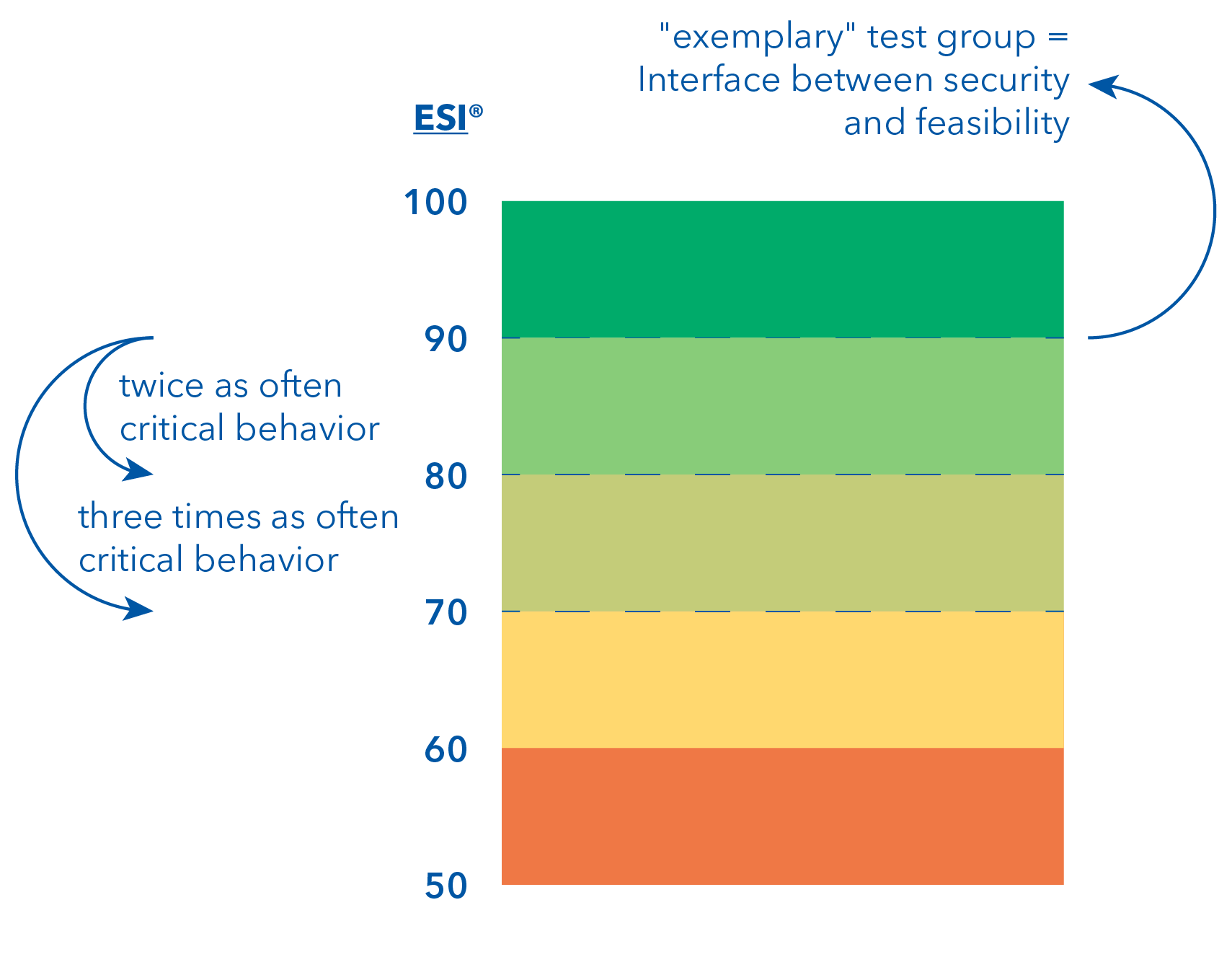
- The behaviour, with regard to the different levels of difficulty, is set in relation to an “exemplary” test group, which is assigned an ESI® of 90.
- If critical behavior is shown twice as often as in the “exemplary” test group, the group achieves an ESI® of 80; if it is shown three times as often, the group achieves an ESI® of 70. And so on…
Critical average level shows need for action
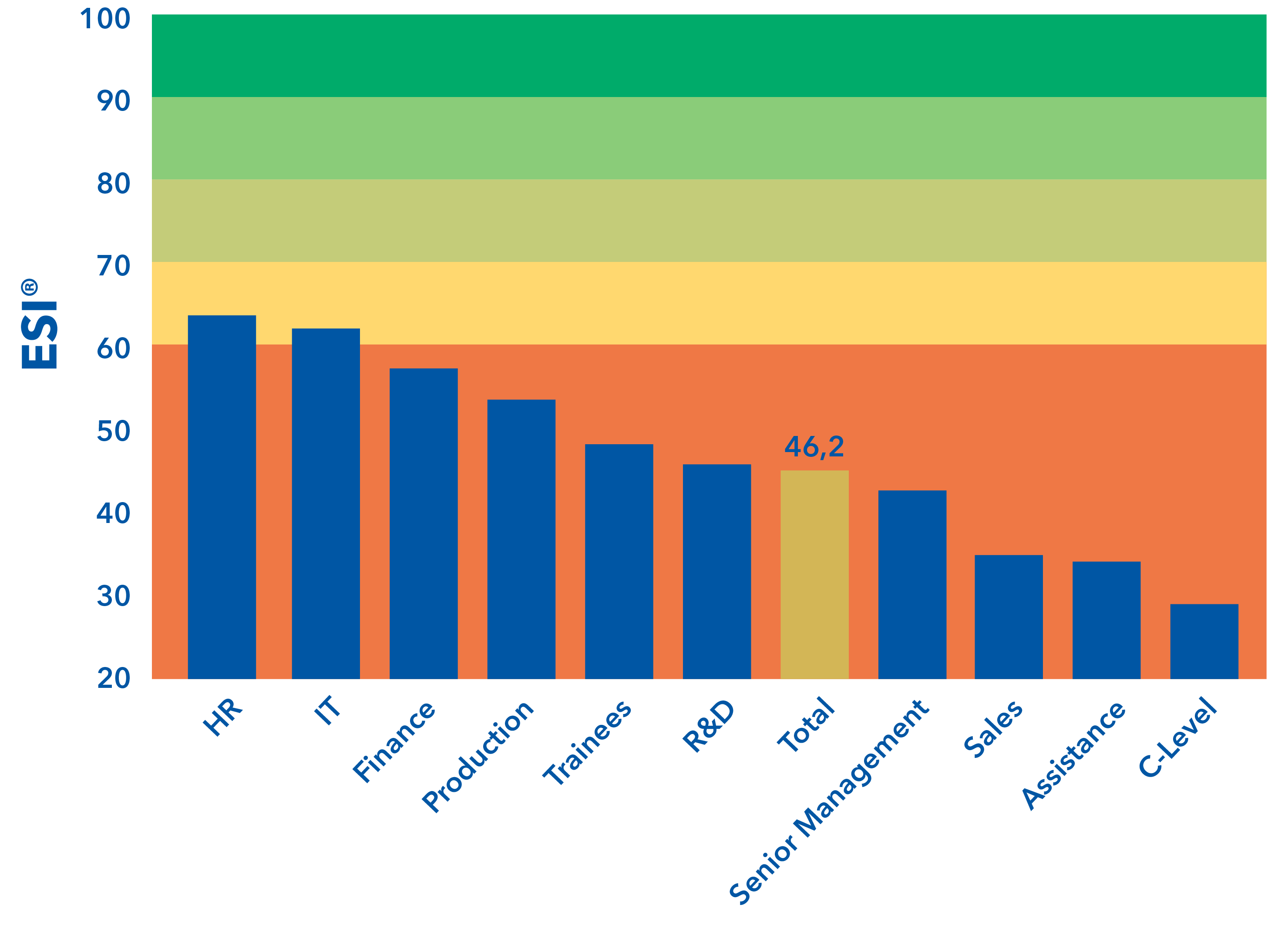
An analysis of more than 75,000 simulated e-mails provides a revealing cross-company insight into the security behaviour of individual departments, as shown in the figure on the right.
All test groups show critical phishing awareness, with an average Employee Security Index of 46.2. While HR, IT and Finance departments perform above average across the company, the departments Sales, Assistence and C-level stand out at the lower end.
The ESI® in the Security Awareness Training
In addition to our phishing simulation, we also use other security awareness measures, such as short videos, face-to-face training and e-learning.
The ESI® thus represents a control instrument with which the security awareness in companies can be continuously monitored. The effectiveness of individual training measures can be reviewed and concrete needs can be identified. The anonymous evaluation of the results on a group basis contributes to employee protection. Communication with both management and staff is facilitated by a tangible key indicator: a quantitative analysis of security awareness offers a direct comparison with other companies in similar industries and can thus be used as a basis for decisions on further investments.
The Target ESI® Security Guarantee from IT-Seal

Did you know that IT-Seal – as the only provider on the market! – gives you a guarantee that the targeted security level will be achieved?
- At the beginning of the training, you specify the desired safety level with the target ESI®.
- We take care in full service to guarantee that this is achieved within 12 months.
- If this is not the case, we will continue to train your employees "free of charge" until the Target ESI® and therefore the desired level of security is reached!
We deliver what we promise!
Our whitepaper about the Employee Security Index (ESI®)
The whitepaper is about the Employee Security Index (ESI®). It provides you with factual and scientifically information about the advantages of our benchmark.
Our whitepaper about the Employee Security Index
The whitepaper is about the Employee Security Index (ESI®). It provides you with factual and scientifically information about the advantages of our benchmark.
Register for the free demo now!
Get to know our Next-Gen Security Awareness Training at Hornetsecurity without obligation. Request your personal demo now for free and learn all about:
- Spear-Phishing-Simulation
- E-Learnings in the Security Hub
- Control Panel
Sounds good? Then take the free trial!
Register without obligation for our demo application:
- Spear phishing simulation
- Trial access to the Security Hub and all e-learnings
- Trial access to the Awareness Manager